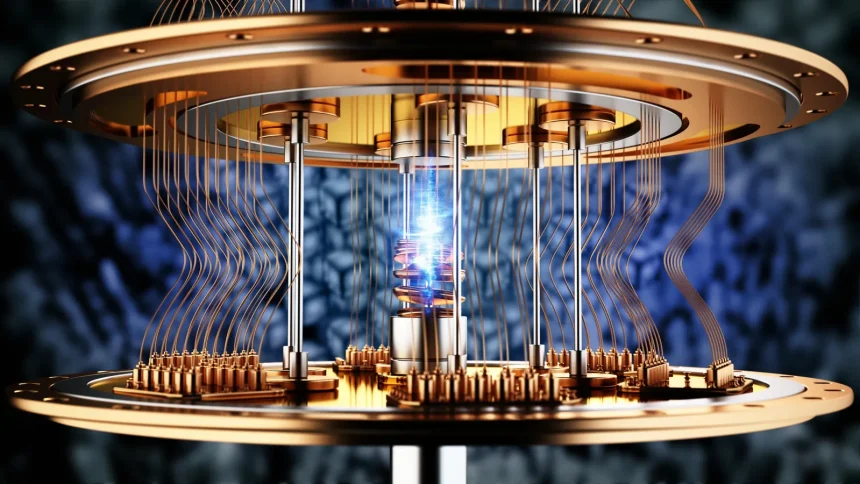
Understanding Quantum Computing and Its Security Impact
Quantum computing is on the verge of reshaping the digital landscape. Unlike classical computers that process bits as either 0 or 1, quantum computers use qubits, which can exist in multiple states at once due to the principles of superposition and entanglement. This unique capability means quantum computers can process vast amounts of data and solve complex problems much faster than traditional systems.
However, this advancement brings new security risks. Many encryption techniques currently in use, including RSA and elliptic curve cryptography, could be broken by a sufficiently powerful quantum computer. This vulnerability puts sensitive data at risk, including financial information, government secrets, and personal records. As quantum technology progresses, organizations must proactively rethink their security postures to ensure the safety of their digital assets.
The Need for Quantum-Resistant Security Solutions
The race toward practical quantum computers has made quantum-resistant security a pressing concern. Organizations that delay preparing for this shift risk having their data exposed when quantum computers become commercially viable. Implementing Future proof Quantum Security solutions can provide a critical layer of defense against these emerging threats and help safeguard information for years to come.
Researchers and industry leaders are actively developing cryptographic algorithms designed to withstand attacks from quantum computers. These algorithms, often called post-quantum or quantum-safe cryptography, are built on mathematical problems believed to be intractable even for quantum machines. The urgency is compounded by the risk of “harvest now, decrypt later” attacks, where adversaries collect encrypted data today with the intent to decrypt it once sufficiently powerful quantum hardware becomes available.
Organizations must begin inventorying their cryptographic assets and identifying systems that rely on vulnerable algorithms. This proactive assessment will help prioritize which parts of the infrastructure need to be updated first. Waiting until quantum computers are mainstream could result in data breaches, regulatory penalties, and significant loss of customer trust.
Post-Quantum Cryptography: Building New Defenses
Post-quantum cryptography consists of algorithms specifically designed to resist attacks from quantum computers. Unlike traditional algorithms that depend on the difficulty of factoring large numbers or solving discrete logarithm problems, post-quantum methods are based on mathematical problems believed to be hard even for quantum machines. The University of Waterloo’s Institute for Quantum Computing is a leading centre for quantum computing research and applications, with active work in quantum-safe cryptography and annual conferences that bring together government, industry, and academia to advance the field.
Several families of post-quantum algorithms are under development, including lattice-based, hash-based, code-based, and multivariate polynomial cryptography. Each has its strengths and trade-offs in terms of computational efficiency, key sizes, and security guarantees. The transition to post-quantum cryptography will be gradual, requiring careful planning, testing, and phased rollouts to minimize disruption to existing systems.
Preparing Infrastructure for the Quantum Shift
Preparing for the quantum era involves more than just updating software. Organizations must conduct a thorough assessment of their current infrastructure to identify all points where cryptographic protections are used. This includes not only obvious systems like VPNs, secure email, and web servers, but also embedded devices, IoT endpoints, and legacy systems that may be difficult to upgrade.
Migration to quantum-resistant algorithms often requires new hardware or firmware updates, particularly for systems with limited processing power. Organizations should develop a phased migration plan that prioritizes high-risk assets and mission-critical systems first. Regular audits, penetration testing, and vulnerability assessments will help confirm that new measures are effective. The National Quantum Initiative announced that NIST has published post-quantum encryption standards that are ready for immediate deployment, and system administrators are encouraged to begin transitioning as soon as possible.
Implementing a Quantum-Ready Security Strategy
A comprehensive quantum-ready security strategy goes beyond adopting new cryptographic methods. It involves a holistic approach that includes employee training, updates to security policies, and continuous risk assessments. All staff, from executives to front-line IT workers, should understand the quantum threat and their role in safeguarding sensitive data.
Developing a clear migration roadmap is essential. This roadmap should outline timelines for replacing vulnerable algorithms, upgrading systems, and testing new solutions. Organizations should also consider the impact on business continuity and plan for possible disruptions during the transition. Pilot implementations can help identify compatibility issues and performance bottlenecks before a full organizational rollout.
The Role of Collaboration and Policy
Addressing the quantum security challenge requires collaboration across sectors. Governments, academic institutions, and private organizations must share knowledge, establish best practices, and coordinate responses to emerging threats. International cooperation is especially important, as quantum attacks can transcend borders and impact global supply chains.
Public policy is playing an increasingly significant role in shaping the future of quantum security. Governments are establishing new standards and regulations for quantum-safe data protection. Compliance with recognized frameworks will help organizations demonstrate their commitment and build trust with customers, partners, and regulators. Regular participation in industry forums and conferences can keep organizations informed of the latest developments and foster valuable partnerships.
Conclusion
Quantum computing is set to transform the digital world, bringing both opportunities and significant security risks. Organizations that act now to prepare for quantum threats will be better positioned to protect their data and maintain trust. By adopting quantum-resistant solutions, following emerging standards, and collaborating across sectors, organizations can build a more secure foundation for the quantum era.
FAQ
What is post-quantum cryptography?
Post-quantum cryptography is a set of cryptographic algorithms designed to resist attacks from quantum computers, ensuring that data remains secure even after large-scale quantum machines become available.
How can organizations prepare for quantum threats?
Organizations should start by inventorying all systems using current cryptographic algorithms, prioritize migration to quantum-resistant alternatives for high-risk assets, and follow the standards being published by bodies such as NIST.
When will quantum computers become a real security threat?
Most experts expect cryptographically relevant quantum computers to emerge within the next decade or two, which means organizations should begin preparing now rather than waiting for the threat to materialize.